Microsoft office is something i guess everybody uses it and knows about it and you are a regular computer user then to somewhat extent you are definitely going to use Microsoft office or any other variant, so in this particular post we want to show you how malicious documents can be analyzed in order to find malicious macro code. so let's start it.
Malicious Samples
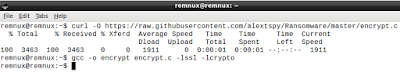
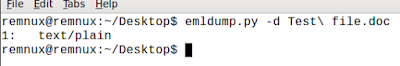
Macro Code is usually written in vba programming for more on it just see the wiki. here i have some malicious sample files which you can get by asking me in comments. they contain some macro code which basically just pings localhost and opens notepad.exe on a windows host.
 |
| malware asking for enable macro |