Microsoft developed OLE technology to combine documents to other objects which hackers also noticed so they tried to use the feature for their own benefit. they tried some micro word 2010 and rich text document also. Let's see how to see a Valid vs a Malicious DOC file.
Are You Ready ?
first create a valid test.doc file which i also created named as Test file.doc i.e micro word document. now its time to perform a quick mimefile analysis on the file,
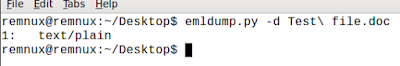 |
| emldump.py -d filename |
once i figured out the file is text/plain i just grabbed the oledump.py and tried to find its headers, macros and all the possible information i can get.
 |
| oledump.py -d filename |
now in order to see what is in the above section i looked at its meta data using oledump.py -M option and below are the results.
 |
| metadata of Given File. |
Infecting the File
now let's infect the file using this exploit.
 |
| malfunctioning the file |
and once it's been altered, now let's examine the same file using above given commands and see what do we get.
 |
| after malfunctioning file |
this is what we get. okay now let's try HexEditor to get what is in the file.
 |
| hexeditor |
can you see the slutfuck written there highlighted ? i didn't wroe that in the original file :|. anyways we can see some garbage, i just found some 414141 sequence in the garbage so it confirms the AAAA usage to write an exploit. Hmmmm.. looks suspicious ??
 |
| 41414141 bof |
okay i've another thing in mind. why don't we try to scan the file using Online virustotal ? let's do it.
 |
| virus-total-scan |
can you see ? im sure enough now you got the point. we can perform more analysis to find out the working and flow of exploit which definitely we're going to do later. hope you enjoyed it. below is the video for dummies.
Please Leave your Suggestion !
Hi All!
ReplyDeleteI'm selling fresh & genuine SSN Leads, with good connectivity. All data are tested & verified.
Headers in Leads:
First Name | Last Name | SSN | Dob | Address | State | City | Zip | Phone Number | Account Number | Bank NAME | DL Number | House Owner
*You can ask for sample before any deal
*Each SSN lead will be cost $1
*Premium Lead will be cost $5
*If anyone wants in bulk I will negotiate
*Sampling is just for serious buyers
==>ACTIVE & FRESH CC FULLZ ALSO AVAILABLE<==
->$5 PER EACH
Hope for the long term deal
For detailed information please contact me on:
Whatsapp > +923172721122
Email > leads.sellers1212@gmail.com
Telegram > @leadsupplier
ICQ > 752822040